Security News 2025 AI Security Solution Report Planning Article

Hello, we are SecuLayer, a company specializing in AI-based security solutions.
Our 'eyeCloudAI' solution has been featured in the [2025 AI Security Solution Report - Special Feature] conducted by Security News.
This report covers in detail the necessity of AI security solutions, the latest technology trends, actual customer success stories, and key factors that customers must consider when implementing these solutions.
We at SecuLayer aim to summarize the key points of this approximately 26-page report to help establish practical criteria for solution implementation.
1. SecuLayer's 'eyeCloudAI' Security Solution (Product and Features)
SecuLayer's AI-based security analysis platform, 'eyeCloudAI', has been introduced as a core component of intelligent security operations.
Product Name: eyeCloudAI (AI Analysis and Support Solution)
Key Features:
An intelligent security analysis platform that automatically analyzes large-scale security events using AI and accurately detects new variant threats.
An 'AI Assistant' based on security-specialized LLM (Large Language Model) provides natural language-based threat analysis and response guidance.
On-premises deployment is possible, allowing for secure operation even in closed network environments.
It is perfectly integrated with the eyeCloudXOAR (SOAR) platform, completing a virtuous cycle automation loop of 'detection-analysis-automated response-reinforcement learning'.
This automation loop improves issues of 'staff shortages' and 'response speed', providing operational efficiency.
2. Current Status of AI Security Technology Application (Stages of AI Integration)
SecuLayer explained how the application scope of AI technology is expanding.
● Paradigm Shift: While early AI focused on detecting abnormal behavior through machine learning or UEBA, it is now explained that the scope has expanded to encompass all security monitoring tasks.
● Transition to AI-Centric Systems: The integration of AI has gone beyond merely adding features; it has reached a stage where the paradigm of security operations is transitioning from 'human-centered manual response' to 'AI-centered intelligent and automated systems'.
● Step-by-Step AI Application (Detection/Analysis/Trust/Automation):
- Detection and Classification: Using deep learning and LM, it accurately detects and classifies new and variant threats that were difficult to identify with existing rule-based systems based on context.
- Analysis and Support: With the integration of generative AI (LLM/RAG) technology, analysts can search for analysis information in natural language, automatically summarize security logs, and the AI Assistant answers natural language queries and automatically generates response reports.
- Trust and Verification: XAI (Explainable AI) visually provides the rationale for why a specific threat was detected, reaching a stage where it secures analyst trust.
- Automation and Optimization: Through AutoML and reinforcement learning, the AI model creation process is automated, continuously learning from operator feedback to optimize model performance.
3. Challenges of AI Adoption (Raising the Black Box Issue)
SecuLayer represented the industry's concerns about the difficulties faced during the process of adopting AI and presented important opinions.
● Issues of Reliability and Transparency: If the basis for AI's decisions cannot be secured, the results cannot be trusted, leading to hesitation in executing response actions based on AI judgments.
● Difficulty in Securing Explainability: It was pointed out that securing 'explainability' to make AI's decisions trustworthy and acceptable was very challenging.
4. Case Studies of AI Security Solution Implementation
SecuLayer has demonstrated tangible results through the establishment of an AI-based smart security monitoring system.
● Client: A public institution
● Necessity: There were limitations in quickly responding to intelligent threats while analyzing more than 400GB of massive security logs daily.
● Implementation and Results:
- By implementing the eyeCloudAI and eyeCloudXOAR (SIEM/SOAR) solutions, a 'smart security monitoring system' was established.
- A customized AI model tailored to the institution was created and applied through integrated learning of datasets, maximizing detection accuracy. As a result, the entire process of detection, analysis, and response to security threats was automated, allowing for the analysis and blocking of tens of thousands of attack attempts within 1 second. During the two-month stabilization period after implementation, hundreds of security threats were perfectly analyzed and blocked daily, establishing an 'advanced security system where AI defends against AI attacks.'
5. Interpretation of CISO Requirements
SecuLayer interpreted the significance of the survey results from Chief Information Security Officers (CISOs) focusing on AI-based detection and response technologies.
● Concerns about Security Gaps: Citing a report stating that "44% of actual security events go uninvestigated due to staff shortages, and among investigated events, 51% remain unresolved," it was analyzed that CISOs are most concerned about this critical security gap.
● Emphasis on AI's Role: "CISOs' focus on AI-based detection and response technologies is because they are the most realistic and powerful alternative to fill security gaps," it concluded.
< Summary of the 2025 AI Security Solution Report >
Ⅰ. AI Security Becomes an Essential Strategy for Survival (Background and Necessity)
1. The Era of AI Threats: Speeds and Scales Beyond Human Capacity
Since the emergence of LLM (Large Language Model), the use of AI in the cybersecurity field has exploded. However, this is also true for attackers, as agile hackers have begun to utilize AI for cyber attacks, presenting a significant security threat.
● Staff Shortages and Security Gaps: As the workload of security personnel increases, the shortage of security talent has made AI a viable alternative. A significant number of actual security events are left uninvestigated or unresolved due to staff shortages, creating critical security gaps.
● Role of AI: AI helps overcome the limitations of existing security solutions by analyzing large-scale data in real-time and learning patterns that are difficult for humans to handle.
2. Evolving AI: Active and Explainable (XAI) Technologies
AI security solutions are evolving beyond merely assisting with alerts to making independent judgments and ensuring transparency.
● Active AI: Active AI goes beyond user responses, taking the initiative to perceive the environment and infer to decide and execute the next steps. This is the core of 'Preemptive Cybersecurity,' which uses AI-based analysis and automation to proactively detect and respond to threats before they occur.
● XAI (eXplainable AI): A technology that explains the rationale and operation of AI's decisions in a way that humans can understand. It enhances the trustworthiness of AI judgments and helps analyze and reduce the basis for false positives in the threat detection process.
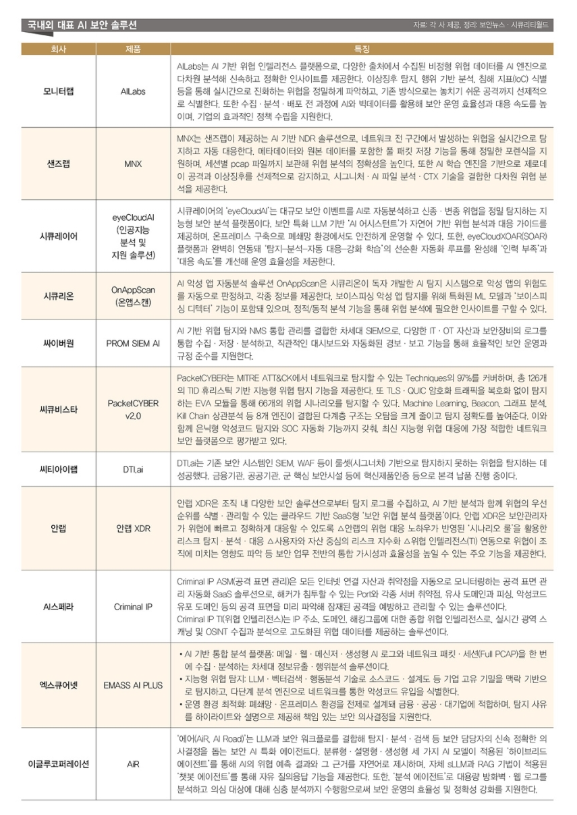
▲Representative AI Security Solutions in Korea and Abroad [Source: Provided by each company, organized by Security News·Security World]
Ⅱ. Core Functions and Customer Value of AI Security Solutions
AI security solutions are integrating technologies to capture both improved detection accuracy and maximized operational efficiency.
1. Enhanced Detection: Generative AI and Ultra-Precise Analysis
● Intelligent Analysis Based on LLM: With the integration of LLM technology, analysts can search for analysis information in natural language, automatically summarize security logs, and generate response reports automatically through the AI Assistant.
● Noise Reduction: AI learns the normal behavior of the system and identifies anomalies, accurately filtering out false positives among numerous alerts, allowing security personnel to focus on 'real threats.'
● Context-Based Leak Prevention: Technologies have emerged that analyze the meaning and relationships of sentences through neural networks that understand context, assessing the risk of corporate confidential information leaks beyond fixed patterns like resident registration numbers.
2. Operational Automation: SOAR and Integrated Monitoring
One of the most important values of AI is automation.
● SOAR (Security Orchestration, Automation, and Response): After threat detection, SOAR automatically executes standardized response procedures (playbooks), dramatically reducing mean time to respond (MTTR) and minimizing human error.
● AI-Driven Systems: Beyond the 'AI-Powered' level where AI supports analysis, there is a demand for 'AI-Driven' systems where AI directly assesses threats and executes responses. SecuLayer describes this as a transition from 'human-centered manual response' to 'AI-centered intelligent and automated systems.'
● XDR Integration: XDR (Extended Detection and Response) integrates data from various areas such as endpoints and networks to perform AI-based analysis, enabling rapid and sophisticated responses even in complex threat environments.
Ⅲ. Key Elements Customers Must Know When Implementing AI Solutions
Customers looking to adopt AI security solutions must clearly understand not only the technical advantages but also the challenges and essential requirements during implementation.
1. Challenges of AI Security (Factors Hesitating Investment)
● High Implementation Costs: According to a survey of security experts, the biggest reason for hesitating to adopt AI solutions is 'high implementation costs (35.4%).'
● Difficulty in Securing Data: The performance of AI models is heavily dependent on the quality and quantity of training data, and creating a reliable dataset requires significant time and effort due to the varying formats of logs from different security devices.
● Lack of Reliability/Transparency: The lack of reliability and transparency regarding AI (26.9%) is also a major reason for hesitating to adopt it. SecuLayer pointed out that securing explainability to trust AI's decisions has been challenging.
2. 'Security for AI' Protecting AI Itself
AI security solutions for safely using AI technology are becoming increasingly important.
● Prompt Protection: The risk of personal and sensitive information leakage through prompts (questions) has increased with the use of generative AI services, making prompt input monitoring, blocking, and masking features essential.
● AI Model Protection: Blocking hacking and data leakage risks that exploit vulnerabilities in AI models has become a core element in protecting corporate assets.
3. Core Support and Success Cases Required by Customers
The items that security experts responded as most needed for the adoption of AI security solutions were
'objective performance comparison data (36.6%)' and 'success cases in the same field (32.0%).'
● Proof of Success Cases: SecuLayer recorded automated results that analyzed and blocked tens of thousands of attack attempts within 1 second by implementing AI/SOAR solutions in public institutions. This demonstrates that AI is the most realistic and powerful alternative to fill security gaps.
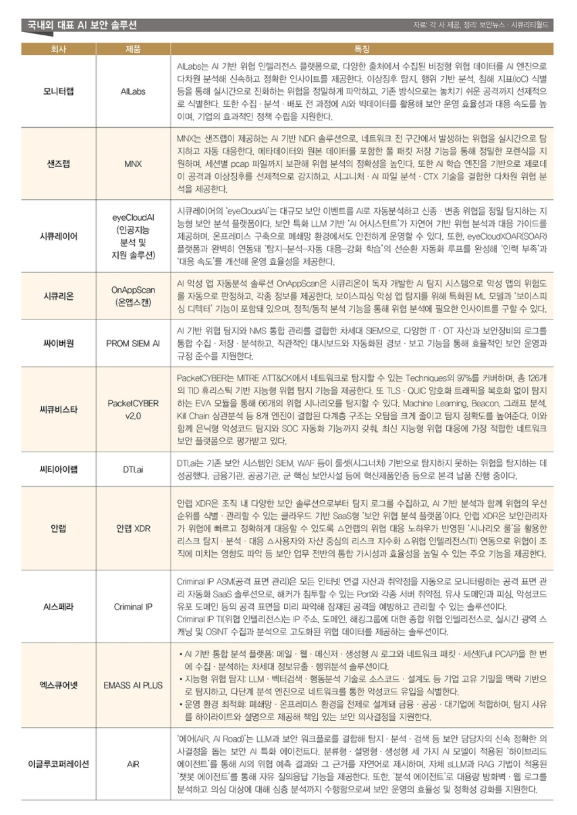
Additionally, to understand how actual security experts perceive AI security, Security World and Security News conducted a survey among security experts from November 18 to 20, 2025. A total of 1,755 security experts from the public (23.4%) and private (76.6%) sectors responded. Below are the detailed results of the survey.
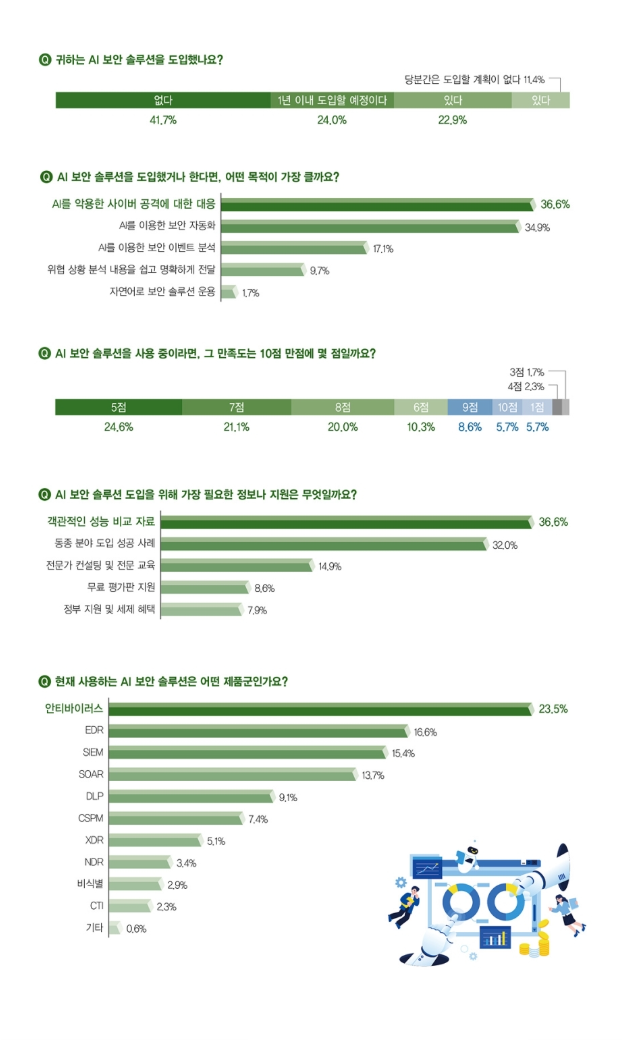
▲Survey of Security Experts on AI Security [Source: Security World·Security News]
4. Future Outlook and Final Selection Criteria for Customers
● Role of AI: Kwon Tae-kyung, Chair of the AI Security Research Committee of the Korean Information Security Association, evaluated that current AI security solutions are not at a level to replace human analysts but will become a 'Powerful Augmentation Tool' that maximizes analysts' capabilities.
● Priority of Security: The Korean Information Security Association emphasized that the development of AI without guaranteed security is like building a house of cards, and AI security is an important factor that should be considered from the development stage, not just added after the system is built.
The items that customers responded as most needed when adopting solutions were 'objective performance comparison data (36.6%)' and 'success cases in the same field (32.0%).'
Therefore, when selecting an AI solution, it is most prudent to choose a solution that clearly shows the basis for AI's judgments based on learning data optimized for our company's environment, and can numerically prove actual operational efficiency and response speed. This report suggests that.
We have explored the necessity of AI security solutions, the latest technology trends, actual customer success stories, and the key elements customers must consider when implementing them.
For more detailed information, please refer to the published special article.
Thank you.
![[Event Sketch] SecuLayer Introduces the eGISEC 2026 Participation Site!](/_next/image?url=https%3A%2F%2Fd1dvcjcxccygto.cloudfront.net%2Fuploads%2Fmig_1775801783179_371718426.jpg&w=3840&q=75)

![[Event Participation News] eGISEC 2026 (14th e-Government Information Security Solution Fair)](/_next/image?url=https%3A%2F%2Fd1dvcjcxccygto.cloudfront.net%2Fuploads%2F1775812276068-981636870.png&w=3840&q=75)